Related Posts
Threat Advisory
Jun 2025
Adarma recently conducted research (a study of 500 C-level executives at UK businesses with over 2,000 employees) aimed at investigating how organisations perceive today’s threats and how prepared they are to respond. We found that 58% of respondents have experienced a ransomware attack, while, unsurprisingly 94% of respondents were either concerned or very concerned about being hit by ransomware.
But what is ransomware and how exactly do varieties of this attack differ and what can we do to be better prepared? The first step is to understand how these attacks work so we, with our partners CrowdStrike, have gathered 15 recent examples of ransomware attacks to explore how they operate.
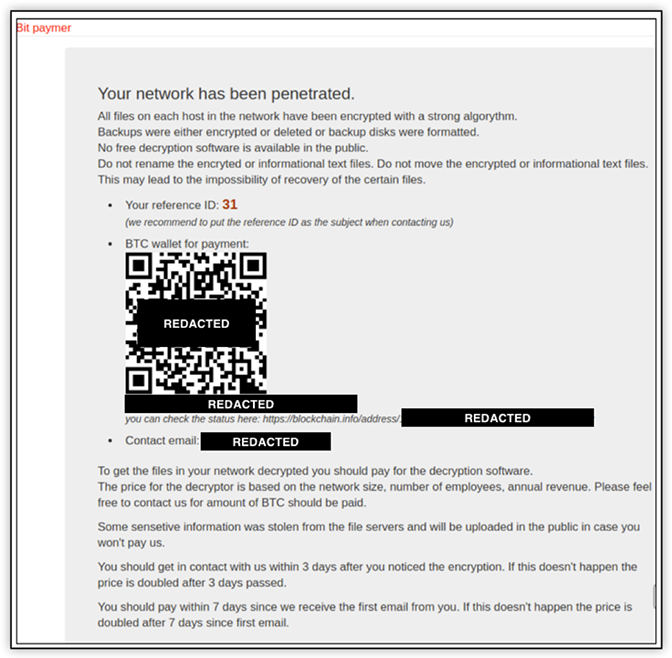
Our threat intelligence team has been tracking the original BitPaymer since it was first identified in August 2017. In its first iteration, the BitPaymer ransom note included the ransom demand and a URL for a TOR-based payment portal. The payment portal included the title “Bit paymer” along with a reference ID, a Bitcoin (BTC) wallet, and a contact email address. An example of this portal is shown below:
Screen lockers virtually disappeared after the introduction of a ransomware group known as CryptoLocker in 2013. CryptoLocker ransomware was developed by the so-called BusinessClub that used the massive Gameover Zeus botnet with over a million infections. The group decided to develop their own ransomware and deploy it to a subset of their botnet’s infected systems. The ransom demand for victims was relatively small — an amount between $100 and $300 USD — and payable in a variety of digital currencies including cashU, Ukash, Paysafe, MoneyPak, and Bitcoin (BTC).
DarkSide ransomware is a Ransomware as a Service (RaaS) operation associated with an eCrime group with operators traditionally focused on Windows machines and have recently expanded to Linux, targeting enterprise environments running unpatched VMware ESXi hypervisors or stealing vCenter credentials. On 10 2021, the FBI publicly indicated the Colonial Pipeline incident involved the DarkSide ransomware. It was later reported Colonial Pipeline had approximately 100GB of data stolen from their network, and the organisation allegedly paid almost $5 million USD to a DarkSide affiliate.
Dharma has been in operation since 2016 under a RaaS model, where developers license or sell ransomware to other criminals who then carry out an attack using the malware. Dharma affiliates do not appear to discriminate among industries.
The original author of Dharma released the source code in 2016 before ceasing activity. Since this threat actor’s departure, Dharma has been marketed and sold by multiple, apparently independent actors, two of which were active in 2019 — and at least one remains active as of January 2020. Separately, while the Phobos ransomware is likely to have been inspired by Dharma, the codebase of Phobos appears separate from Dharma.
While the first known victims of DoppelPaymer were targeted in June 2019, but earlier builds of the malware were recovered dating back to April 2019. These earlier builds are missing many of the new features found in later variants, so it is not clear if they were deployed to victims or if they were simply built for testing.
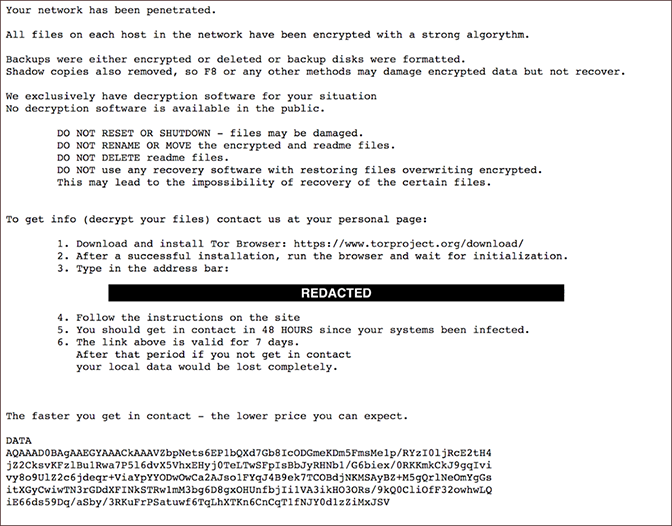
The ransom note used by DoppelPaymer is similar to those used by the original BitPaymer in 2018. The note does not include the ransom amount; however, it does contain a URL for a TOR-based payment portal, and instead of using the keyword KEY to identify the encrypted key, the note uses the keyword DATA as shown below.
GandCrab has established itself as one of the most developed and prevalent ransomware families on the market. Development of the ransomware itself has been driven, in part, by PINCHY SPIDER’s interactions with the cybersecurity research community. GandCrab contains multiple references to members of the research community who are both publicly active on social media and have reported on the ransomware.

PINCHY SPIDER has continued to promote the success of its ransomware in criminal forum posts, often boasting about public reporting of GandCrab incidents. In February, PINCHY SPIDER released version 5.2 of GandCrab, which is immune to the decryption tools developed for earlier versions of GandCrab and in fact, was deployed the day before the release of the latest decryptor.
Recently PINCHY SPIDER has also been observed advertising for individuals with remote desktop protocol (RDP) and VNC (Virtual Network Computing) skills, and spammers who have experience in corporate networking.
Maze ransomware is a malware targeting organisations worldwide across many industries. It is believed that Maze operates via an affiliated network where Maze developers share their proceeds with various groups that deploy Maze in organisational networks. Maze operators also have a reputation for taking advantage of assets in one network to move laterally to other networks.
MedusaLocker is a ransomware family that was first seen in the wild in early October 2019. In January 2020, a fork of MedusaLocker named Ako was observed, which has been updated to support the use of a Tor hidden service to facilitate a RaaS model. Operators of the Ako version of the malware have since implemented a DLS (see below)
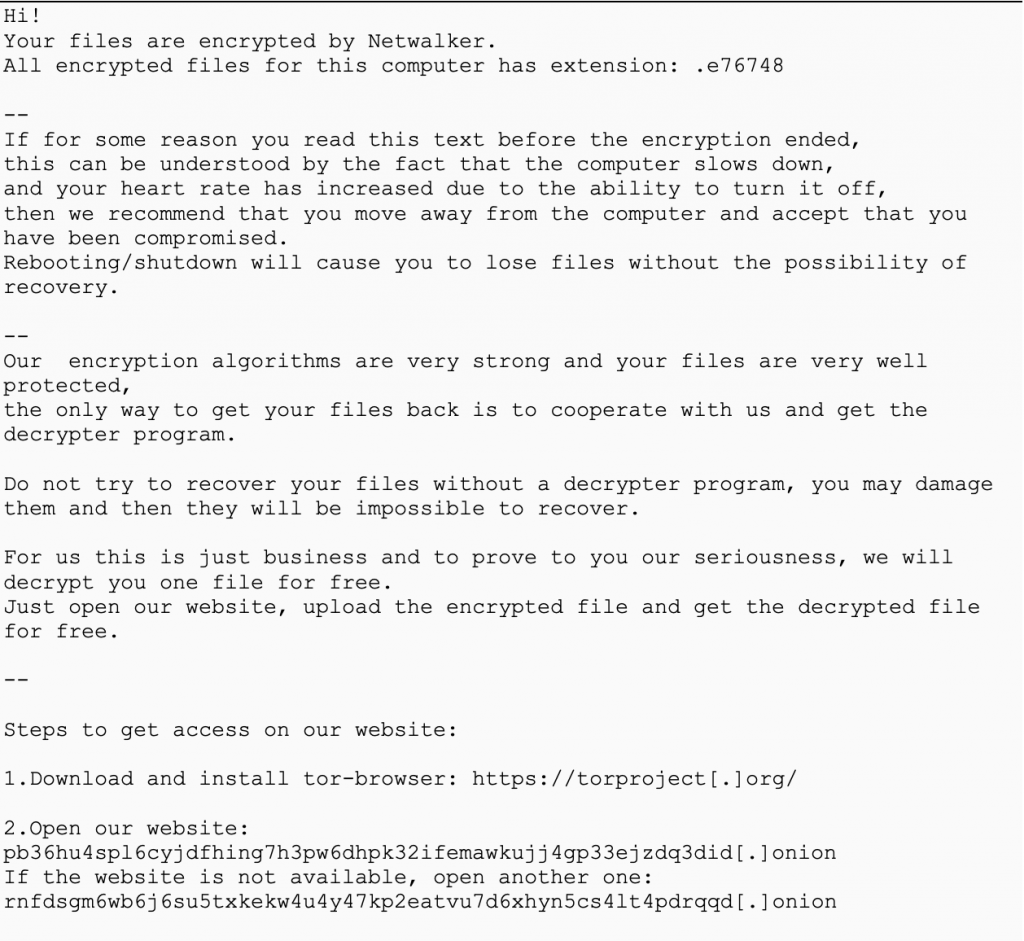
NetWalker is ransomware written in C++ and advertised as a RaaS on forums by a user known to be part of a group designated as CIRCUS SPIDER.NetWalker encrypts files on the local system, mapped network shares and enumerates the network for additional shares, attempting to access them using the security tokens from all logged-in users on the victim’s system.
Below is an example of their ransom note:
NotPetya is a ransomware variant of Petya. First detected in 2017 rapidly infiltrating systems across multiple countries. What’s particularly nasty about this family of ransomware is its use of stealthy propagation techniques that allow it to swiftly move laterally to encrypt other systems across an organisation. NotPetya ransom notes have demanded $300 USD for each infected machine.
Discovered in 2016, Petya ransomware encrypts the Master File Table (MFT) and the Master Boot Record (MBR), making it impossible for you to access anything on the drive. Often it is launched with another exploit call Mischa, so that if Petya lacks the privileges necessary to gain access to the MFT or MBR, Mischa is enabled to encrypt files one by one
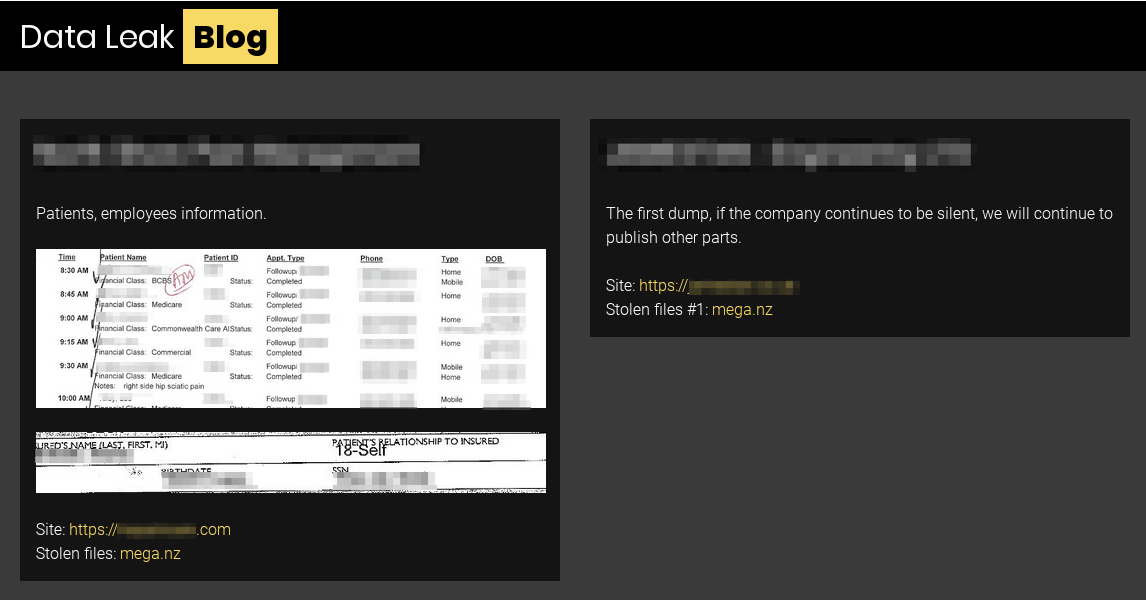
On December 9, 2019, a vendor of PINCHY SPIDER’s REvil RaaS posted a threat to leak victim data to an underground forum. This is the first time it has been observed the group or their affiliates making such a threat, and it appeared to be in frustration over failing to monetise compromises at a U.S.-based managed service provider (MSP) and a China-based asset management firm. Since then, affiliates of PINCHY SPIDER have posted data on more than 80 victims.
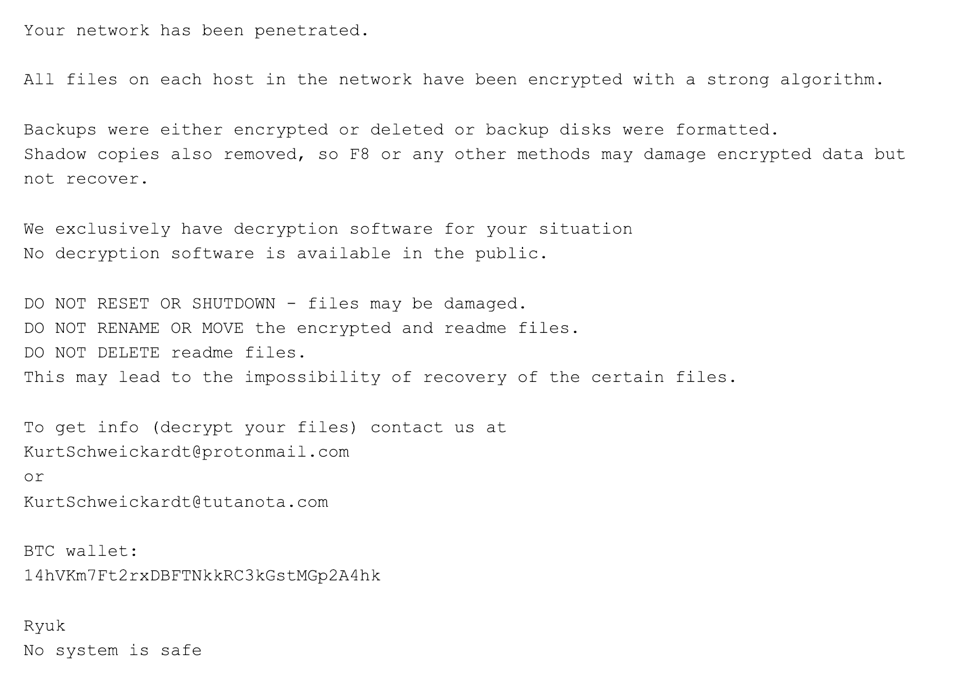
Ryuk is specifically used to target enterprise environments. Code comparison between versions of Ryuk and Hermes ransomware indicates that Ryuk was derived from the Hermes source code and has been under steady development since its release. Hermes is commodity ransomware that has been observed for sale on forums and used by multiple threat actors. However, Ryuk is only used by WIZARD SPIDER, and, unlike Hermes, Ryuk has only been used to target enterprise environments.
Here’s an example of a Ryuk ransom note:
Developed and operated by the cyber adversary, BOSS SPIDER, SamSam has been observed using unpatched server-side software to enter an environment. Most notably, SamSam was behind the 2018 ransomware attack on the city of Atlanta, Georgia. The attack left 8,000 city employees without their computers and citizens were unable to pay their parking water bills and parking tickets.
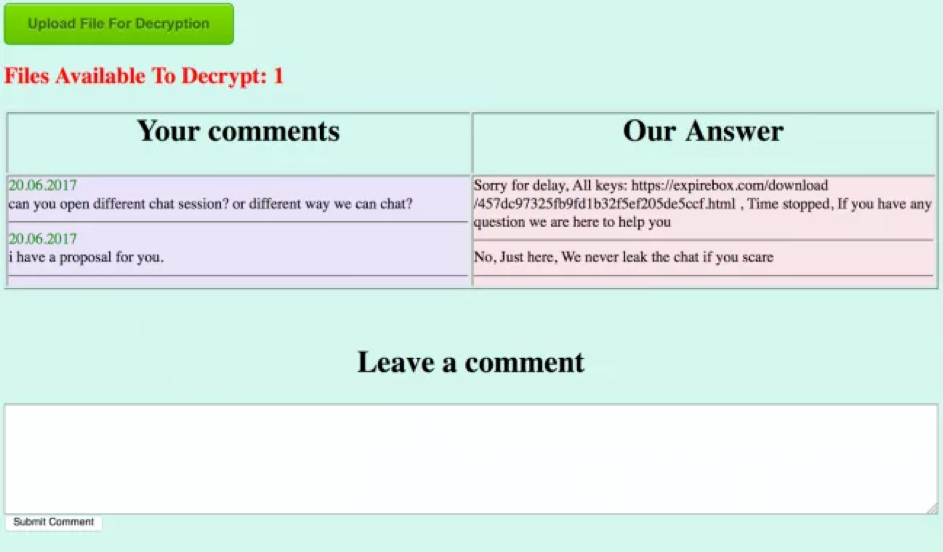
Below is an example of a SamSam operator’s response after the ransom has been paid. The response typically includes a URL for the victim to download decryption keys.
Also referred to as WCry, WanaCrypt, or Wanna, WannaCry was identified in May 2017 during a mass campaign affecting organisations across the globe. WannaCry has targeted healthcare organisations and utility companies using a Microsoft Windows exploit called EternalBlue, which allowed for the sharing of files, thus opening a door for the ransomware to spread.
To find out more about Adarma’s cyber security services and how we can help prepare and protect your organisation against ransomware attacks, please Contact us.
Stay up-to-date with the latest threat insights from Adarma by following us on Twitter and LinkedIn.
An error has occurred, please try again later.An error has occurred, please try again later.

